25 Jun 3 mistakes companies make with disaster recovery planning
If a malicious cyber attacker, utility outage or other type of threat impacted your business, would you be ready to respond and recover? Ensuring disaster recovery preparedness is more pertinent than ever before, now that there are a bevy of factors that could lead to a system outage or downtime. In these instances, it’s critical that companies can leverage backup data to keep operations running smoothly.
When it comes to disaster recovery planning, however, there are a few common mistakes to be aware of and work to avoid. Let’s take a look at these missteps, as well as how the National Institute of Standards and Technology’s Framework or Improving Critical Infrastructure Cybersecurity works into the equation.
Mistake #1: Not understanding the scope and importance of disaster recovery planning
According to Network Computing, as many as 50 percent of all organizations don’t currently have a disaster recovery plan in place, leaving them unprepared to address and recover from a data breach, downtime or other type of disaster.

As many as 50 percent of today’s businesses don’t have a disaster recovery plan in place, leaving them unprepared to respond to an incident.
Herein lies one of the first mistakes companies make with their disaster recovery planning. It’s imperative that organizational and IT leaders understand just how critical it is for them to formulate a response and recovery plan, as well as which assets should be prioritized in such plans.
Mistake #2: Not using available guidelines and standards
The NIST Cybersecurity Framework includes five key functions, including:
- Identify
- Protect
- Detect
- Respond
- Recover
It was first introduced in 2013, with the most recent version released in April 2018. The Framework leverages industry-standard guidelines and practices to help identify gaps in security, protect key infrastructure assets, detect any security anomalies or suspicious activity, respond to any cybersecurity instances and recover from these events.
In this way, the Framework can represent a key asset to reference during the establishment of a disaster recovery plan. Response and Recovery Planning are included as categories under both the Respond and Recover functions. IT and organizational stakeholders should be sure to utilize the NIST Framework, and other standards to help inform and guide their efforts.
Not taking advantage of such resources can result in essential elements being overlooked, making the business unprepared to respond and recover from threats.
Mistake #3: Not testing the plan ahead of use
Once the plan has been established, it’s important that the IT team works with other stakeholders to test the plan and ensure there are no gaps or processes that need adjustment. GS Khalsa, VMware senior technical manager, told Network Computing that while this can be difficult given the complexity of infrastructure systems, having a virtual environment to use for testing purposes can help ease the burden.
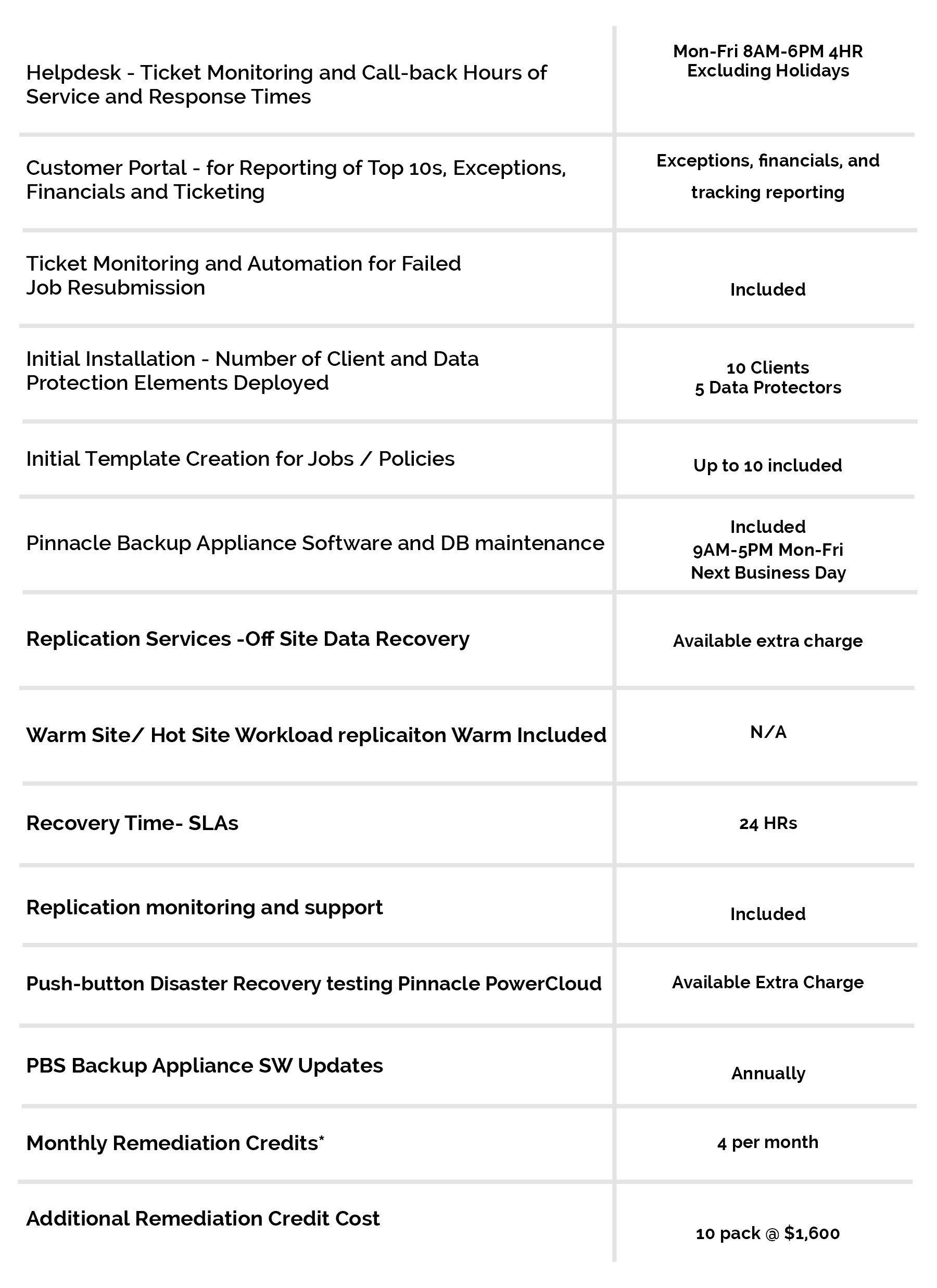
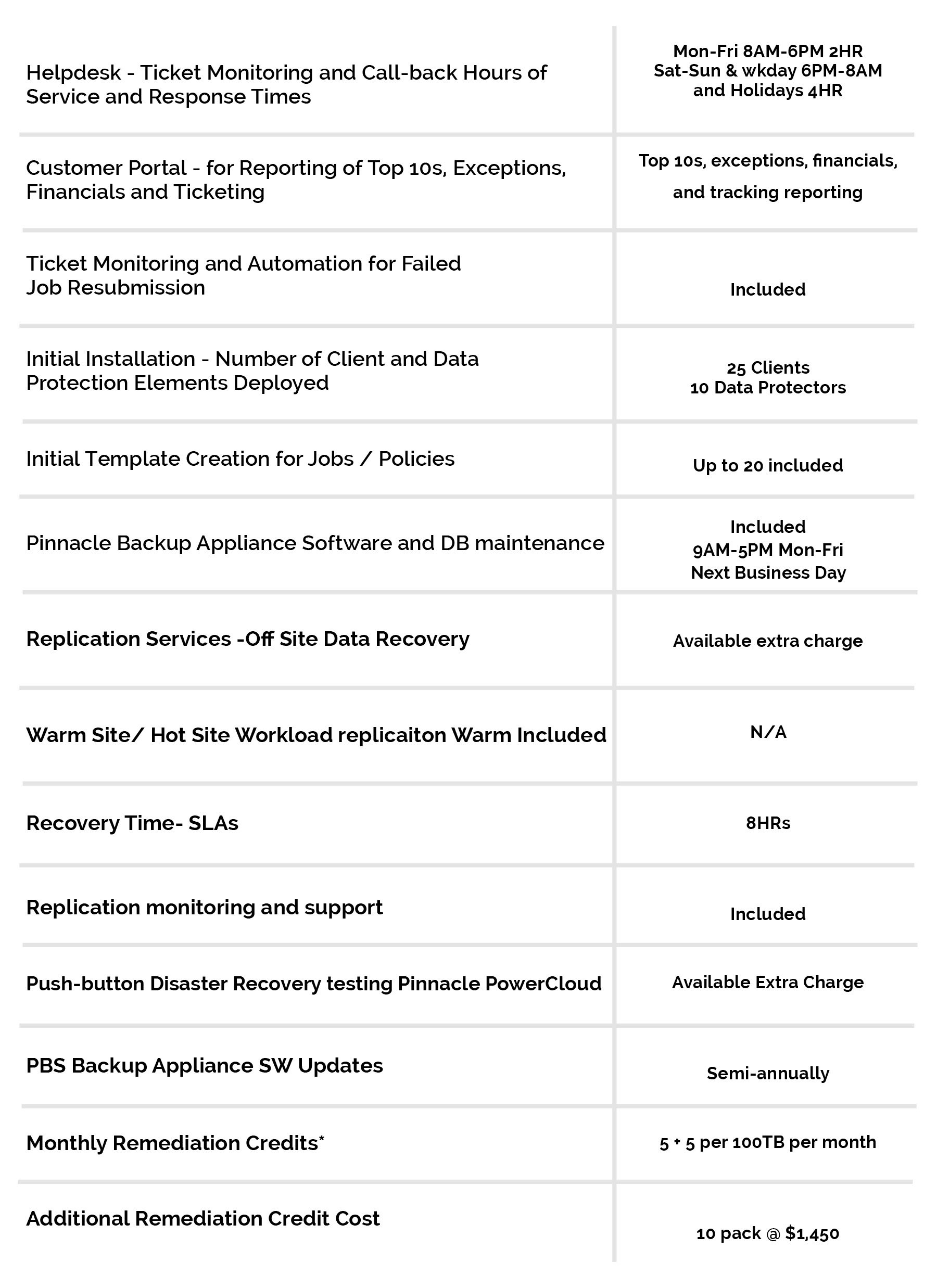
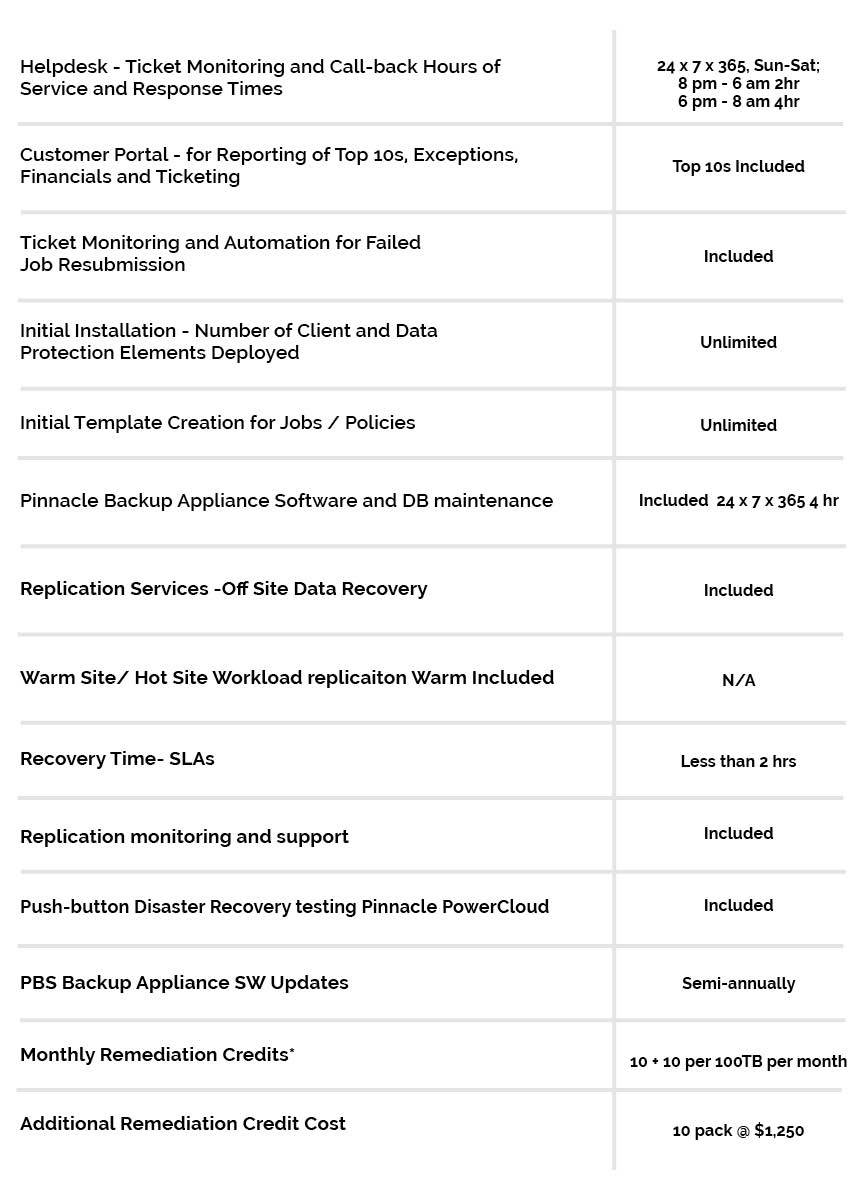
In addition to using a virtual environment to support testing, organizations should also consider making advanced Backup and Recovery as a Service (BRaaS) part of their disaster recovery planning. Such solutions ensure that companies have expertly managed resources to fall back on and recover post-disaster.
To find out more about how BRaaS can help with disaster recovery, connect with the experts at Pinnacle today.