Protecting sensitive data is imperative and has severe consequences if information security is compromised. Whether you represent a financial services company, healthcare facility, a utilities provider or another type of organization, you need a proactive, customized and reliable approach to thwart the constant, increasingly sophisticated threats for peace of mind through data security.
Information Security Solutions
Safeguard the critical data assets your company captures, records, stores and shares every day. Our IT security solutions include best-of-class security technologies, such as next generation firewalls, intrusion prevention systems, data leak prevention, malware defense, content filtering, security monitoring/forensics, and mobile device security. Regardless of the ultimate solution, our singular focus as your information security consultant is minimizing the potential risks to your organization by protecting your information – and information systems.
Data Confidentiality
Gain the assurance that information is accessible only to designated individuals.
Data Integrity
Gain protection of your enterprise data from forgery or alteration by unauthorized parties.
Data Availability
Ensure that critical information and services will be accessible to the people who need it, when they need it.
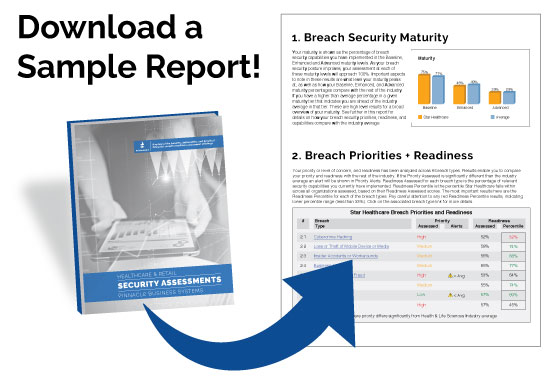
Are you breach-proof?
We offer a Security Readiness Assessment + Report for all industries, that are complimentary, can be done in 1 hour over the phone or in person, prioritizes 8 breach types, and has 42 breach security capabilities from the maturity model. Here’s a little more about what to expect from our assessment and report or contact us to learn more!
- Non-intrusive, timesaving, fully effective, comprehensive and completely confidential
- Identifies where the client is over-or-under prioritizing types of breaches
- Avoid breaches and associated business impact/disruption
- Regulatory compliance, avoiding audits and non-compliance penalties
- Visibility into how they measure up with peers
- Avoid the dreaded headlines – damaged reputation
Our solutions address security challenges you have
and anticipate others you haven’t considered.
For example, your concerns may include:
Leaks of sensitive or confidential data from your environment
Securing and protecting your virtual server or desktop environment
The ability to detect and respond if a system is compromised
Safeguarding critical web-based applications, databases and file servers
The complexities of mobile device security, including employee-owned devices