26 Jun Weaknesses in health care system and device security
A range of recent technological advances have been centered around the health care industry. New approaches and devices are paving the way for more efficient, advanced and informed patient care, leveraging things like connected medical devices and electronic health record systems.
At the same time, though, it is these key systems and endpoints that are creating security weaknesses at health care institutions.
Maintaining privacy within EHRs
One of the most expansive shifts seen in the industry in the last decade or so is the migration to electronic health record systems, or EHRs. Digital record systems ensure that medical personnel have streamlined access to patient data, and can use these details to prescribe the right care within that moment.
It isn’t surprising, however, that these EHRs are also attractive to malicious hackers.
“As EHRs mature and collect vast amounts of data, keeping this data safe as adept cybersecurity threats increase must remain at the forefront,” said Kris Wilson, chief information officer at Hilo Medical Center in Hawaii. “Educating staff on the proper use of hospital systems and safeguards within your EHR to limit the amount of data accessible is a good start to overcoming this challenge.”
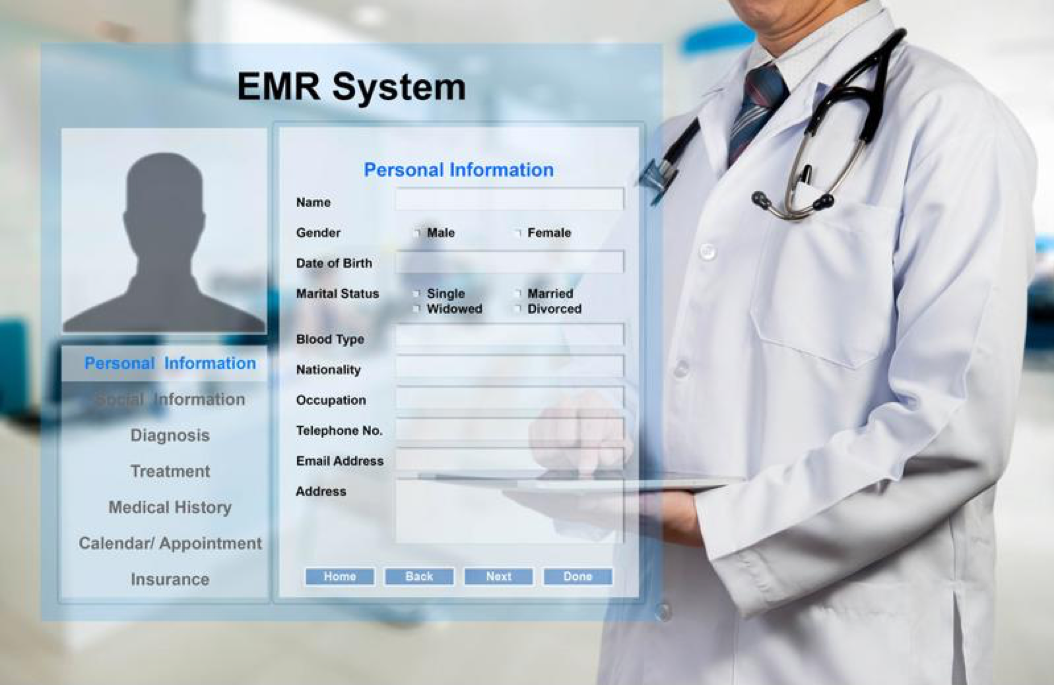
Electronic medical records, which contain a wealth of personal details, are attractive targets for hackers.
Because EHRs contain so many personal and sensitive patient details – including names, mailing addresses, payment information and medical condition data – it’s imperative that these systems are properly safeguarded to deter any unauthorized access.
Potential patient device vulnerabilities
In addition to the system being used to contain patient information, risks are also emerging in connection with sensitive medical devices including implated and wearable devices.
As WIRED contributor Lily Hay Newman noted, security has historically been “lax” on embedded medical devices in particular. But the consequences of a hacker breaching and taking control of this type of endpoint could easily be deadly for the patient depending on its proper operation.
Making matters worse is the fact that this problem appears to be growing in both scope and public awareness. As recent Trend Micro research discovered, there are over 36,000 connected health care devices in the U.S. that can be easily identified via Shodan, a search engine for connected devices.
“There are over 36,000 connected health care devices in the U.S.”
“Hacked medical devices make for scary headlines,” Newman wrote. “Dick Cheney ordered changes to his pacemaker to better protect it from hackers. Johnson & Johnson warned customers about a security bug in one of its insulin pumps last fall. And St. Jude has spent months dealing with the fallout of vulnerabilities in some of the company’s defibrillators, pacemakers and other medical electronics.”
Taking steps to ensure proper security
As experts note, some of these data protection issues are simpler to address than others. Older, connected medical devices, for example, must be patched and updated to guard against newer threats. And manufacturers of emerging devices should incorporate more robust security from the time of development.
EHR security, on the other hand, falls to the individual organization to protect. One of the best ways to ensure this sensitive information is properly safeguarded is to leverage expert, managed solutions to support data confidentiality, data integrity and data availability.
To find out more about safeguarding your health care organization’s critical IT assets, connect with the experts at Pinnacle today.