19 Mar Top 5 Essentials to Consider with Information Security
In today’s advanced, technological landscape, data and informational assets are more important – and more valuable – than ever before. At the same time, there are plenty of malicious actors vying to snoop and steal company intellectual property and other data. This makes information security an absolutely critical pursuit, and there are a few essentials to consider with any data protection strategy:
Access management
One of the first set of safeguards to put in place are access controls that help ensure only authorized employees and partners are able to read and utilize company informational assets. As Gartner pointed out, elements including overarching digital innovation coupled with the increasing shift of workloads, users, and applications to cloud platforms are having a heavy impact on access management.
Now, IT and security stakeholders must be more careful than ever before to guarantee they follow best practices for access controls. Managers should check that employees utilize unique password credentials that can’t be easily guessed, and that these are changed on a regular basis. It’s also imperative that users don’t leverage the same credentials for different accounts, as this can cause a domino effect should one account become compromised.
Encryption
Once access controls are in place, it’s time to safeguard the data itself. One of the most robust ways to do this relies on strong encryption for data at rest, as well as information in transit. Encryption ensures that should a malicious actor breakthrough access controls and other protections, he or she won’t be able to read or make use of the company’s sensitive data.

Robust access management can be an important line of defense against infection and attack.
Threat monitoring
Monitoring the various environments the company uses for its most critical business tasks is also essential for information security. Monitoring solutions check the network, storage, servers, cloud and other environments for known threats and vulnerabilities, enabling the security team to work proactively to prevent these infections from impacting their data assets.
Currently, malware is only on the rise – 2017 saw the discovery of a new malicious sample nearly every four seconds.
Patch management
In addition to monitoring for threats, it’s also important to ensure that all software is completely up-to-date and patched against the most current security risks. Any delay in installing security patches could provide just the window hackers need for an attack. As NetworkWorld pointed out, it’s important to patch on and off-premises systems, and to check for weekly patches from Microsoft and other technology vendors.
“2017 saw the discovery of a new malicious sample nearly every 4 seconds.”
Securing the cloud
Now that the cloud plays a considerable role in enterprise infrastructure, it’s imperative that protections of this platform are a top security priority. Elements including access controls and encryption can help safeguard data stored and accessed in the cloud. CSO contributor Rahul Pangam also suggested including a deletion policy for the customer and other sensitive data to make sure that the business doesn’t store details longer than necessary. It’s also important to work with the cloud provider to help meet compliance needs in an end-to-end manner.
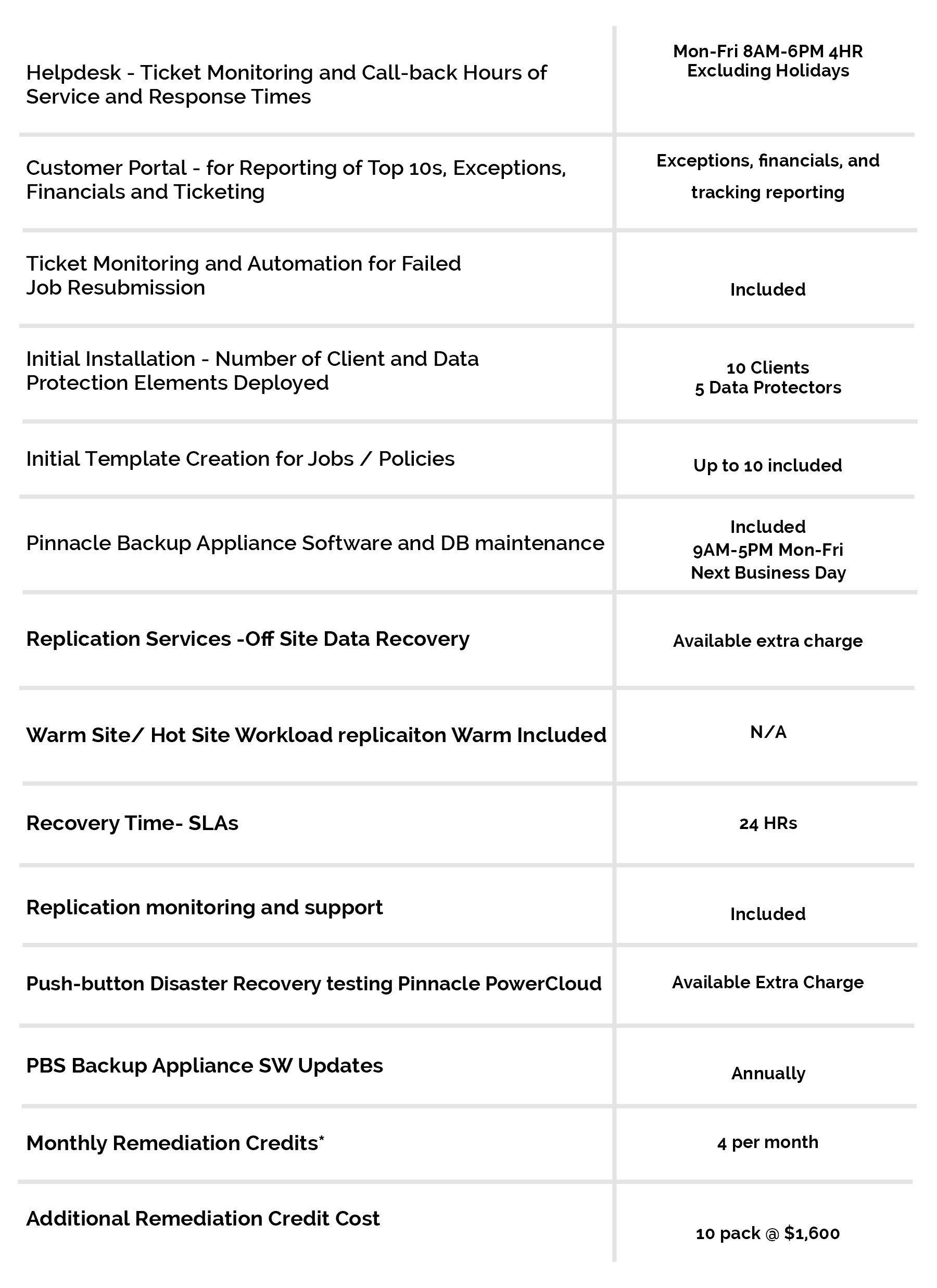
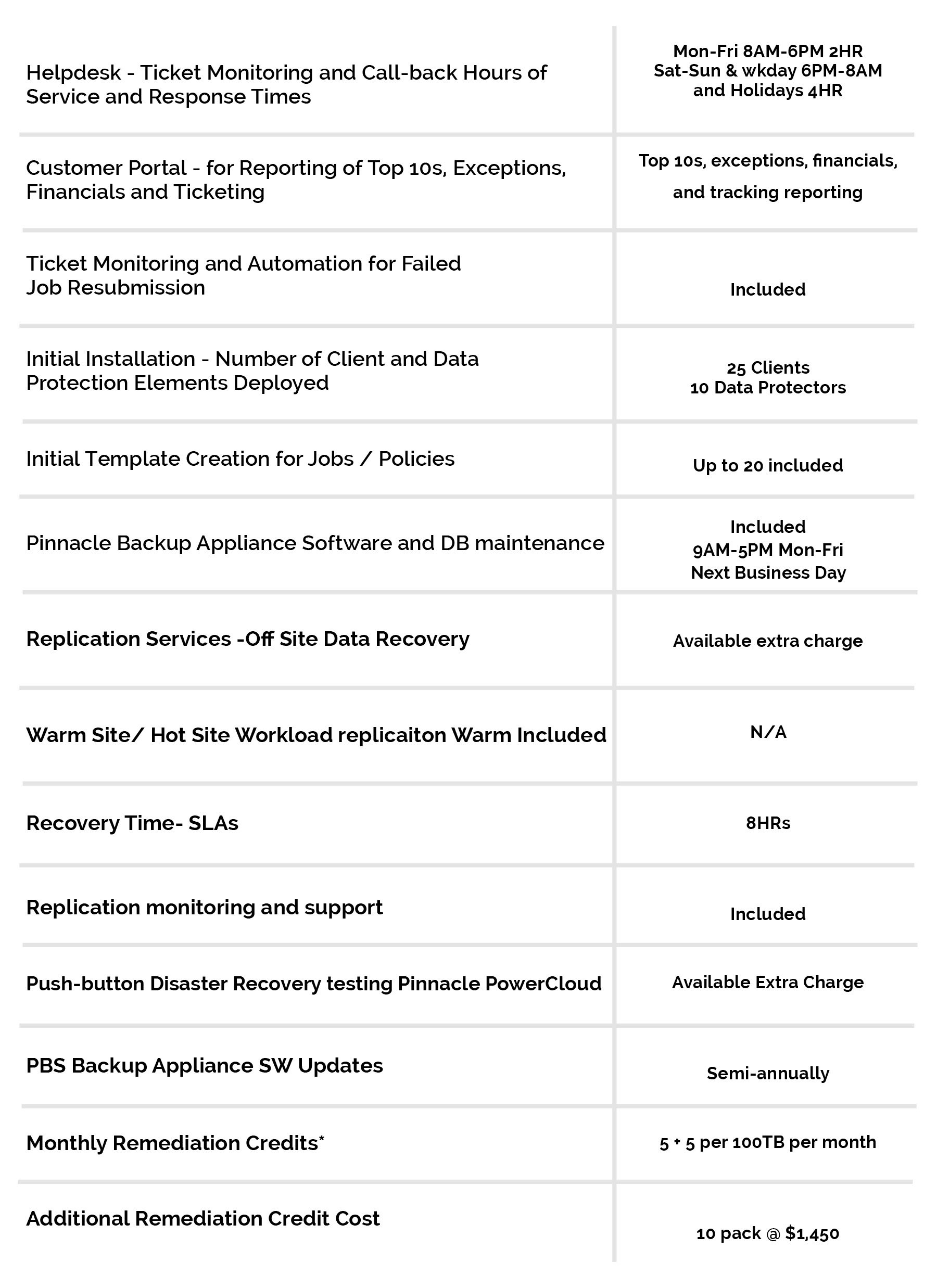
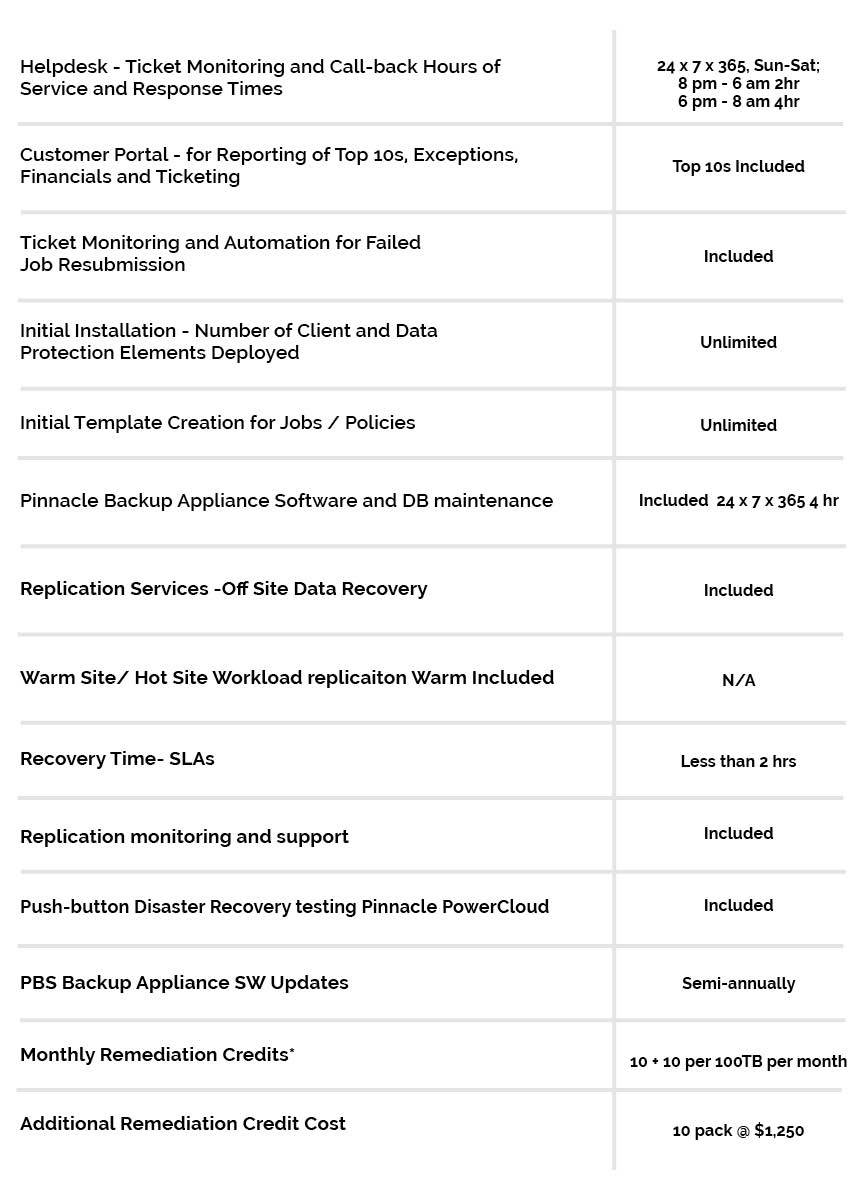
Pinnacle combines the power of cloud and security with its robust PowerCloud and BRaaS solution. This advanced system leverages automation to ensure continuous and up-to-date backup and recovery. In this way, businesses can further ensure the protection of their most crucial assets, even in the face of a disaster.
To find out more about the top considerations for information security, connect with the experts at Pinnacle today.